Home Blog Effective Risk Mitigation Strategies: Safeguarding Your Projects and Organization
Effective Risk Mitigation Strategies: Safeguarding Your Projects and Organization

Risk Management Solutions – Implementing a Risk Mitigation Strategies
Every project is a journey through uncertainty, but ignoring potential problems isn’t a strategy—it’s a gamble. In today’s volatile business environment, crossing your fingers and hoping for the best is a recipe for disaster. Proactive Mitigation Planning is no longer just an optional safety net; it is a fundamental requirement for business survival and growth.
Consider the classic real-world case of the year 2000 Philips microchip plant fire in New Mexico. Both telecom giants Nokia and Ericsson relied heavily on this single plant. When the fire halted production, Ericsson passively waited for the issue to resolve, taking a massive business risk. The result? Ericsson lost an estimated $400 million in sales and was eventually forced out of the standalone handset market. Nokia, however, immediately activated its Risk Mitigation Strategies. They monitored the supply chain daily, instantly secured alternative suppliers, and even redesigned their chips to fit different factories. Because of this proactive risk response, Nokia didn’t just survive the crisis—they capitalized on their competitor’s failure and increased their global market share from 27% to 30% that very year.
This guide provides a definitive overview of the Risk Mitigation Strategies that separate market leaders from cautionary tales. Let’s dive into the specific, actionable steps you must take to lessen the impact or likelihood of a negative event before it occurs, turning unpredictable threats into manageable variables.
What is Risk Mitigation?
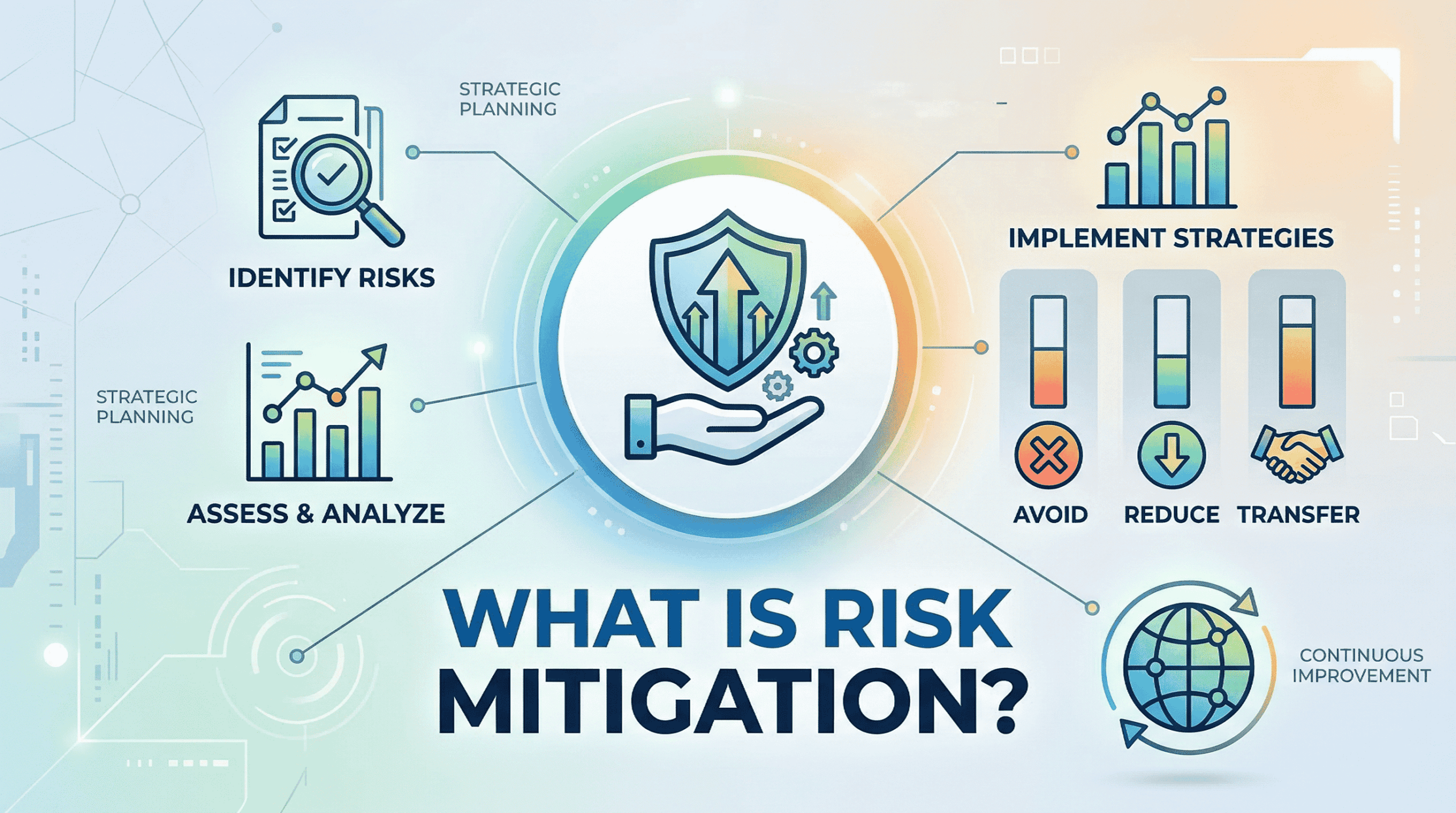
At its core, Risk Mitigation is the action-oriented phase of your overall Risk Management plan. While “risk management” refers to the broad, overarching framework of identifying, assessing, and monitoring threats, mitigation is where the actual work happens.
It is the specific process of developing and deploying preventative actions to reduce either the likelihood of a negative event occurring or the severity of its impact if it does happen. When a high-priority business risk is identified—such as a supply chain failure, a sudden market shift, or a cybersecurity breach—your Risk Mitigation Strategies are the concrete, tactical steps you take to soften the blow or avoid the disaster entirely.
In short: If risk management is the radar system that spots the incoming storm, risk mitigation is the act of boarding up the windows and securing the foundation before it hits.
The Relationship: Risk Mitigation vs Risk Management (Clearing the Confusion)
To build a resilient organization, it is vital to understand the distinction between these two frequently confused terms. Risk Management is the broad, overarching umbrella that covers the entire lifecycle of dealing with business uncertainty. It serves as the comprehensive, strategic framework your organization uses for continuous risk identification, risk assessment, and ongoing monitoring to spot any potential business risk on the horizon.
Conversely, Risk Mitigation is the critical, active risk response phase that lives inside that broader management framework. Focusing exclusively on negative threats, it represents the tactical execution phase where you deploy specific preventative actions and Mitigation Planning to either lower a risk’s probability or reduce its severity. Ultimately, you cannot successfully apply effective Risk Mitigation Strategies without the strong, guiding structure of a complete risk management system to tell you where to aim.
Effective Risk Mitigation Strategies – Steps to Implement Risk Mitigation
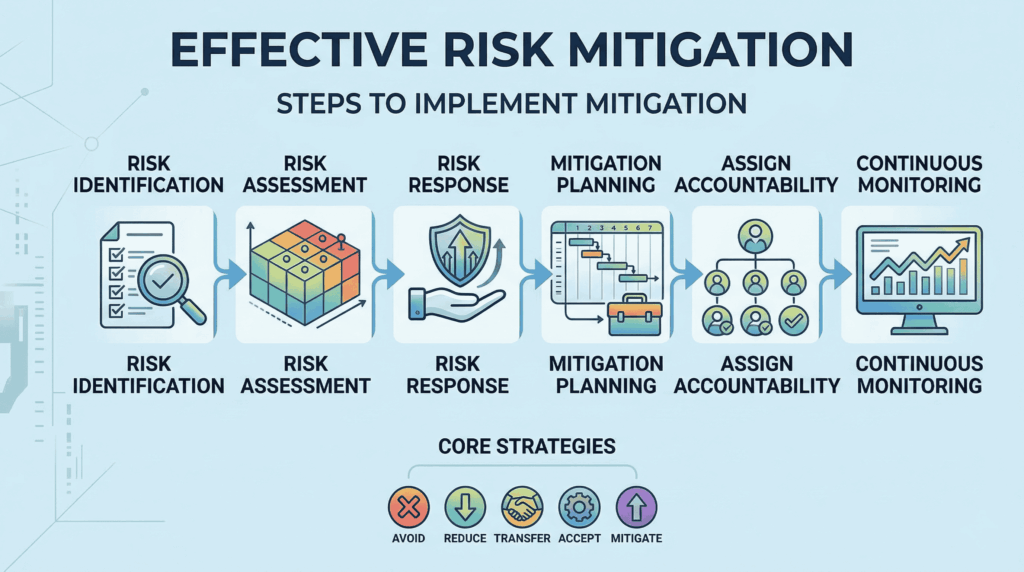
Understanding your threats is only half the battle; the real work lies in execution. Executing an effective risk response plan is a continuous, logical cycle rather than a one-time checklist. To protect your organization from a catastrophic business risk, you must transform your analysis into a structured, repeatable implementation process.
Here are the six essential Risk Management Strategies and steps required to effectively implement your mitigation plan:
- Risk Identification: The cycle always begins with visibility. As covered previously, this is the ongoing process of listing all potential internal and external threats to your project or organization.
- Risk Assessment: Once identified, you must objectively prioritize these threats using a Risk Matrix, evaluating them strictly by their Probability and their potential Impact.
- Risk Response (Strategy Selection): This is the pivot point where analysis becomes action. Based on your assessment and your organization’s risk tolerance, you must select the appropriate overarching strategy to handle each high-priority threat (we will break down the five core strategies in the next section).
- Mitigation Planning & Preventative Actions: With a strategy selected, you must define the specific, mandatory preventative actions required. This step involves creating a clear, actionable roadmap detailing exactly what will be done, when it will be done, and what resources are required.
- Assigning Accountability: A mitigation plan without designated owners will fail. Every single identified risk and its corresponding preventative tasks must be assigned to a specific individual or team who is held accountable for its execution.
- Continuous Monitoring and Review: The business landscape is dynamic, and new threats emerge daily. Your Mitigation Planning is a living document that requires regular review cycles to ensure your chosen Risk Mitigation Strategies remain effective and relevant.
The Core 5: Types of Risk Mitigation Strategies (The Actionable Steps)
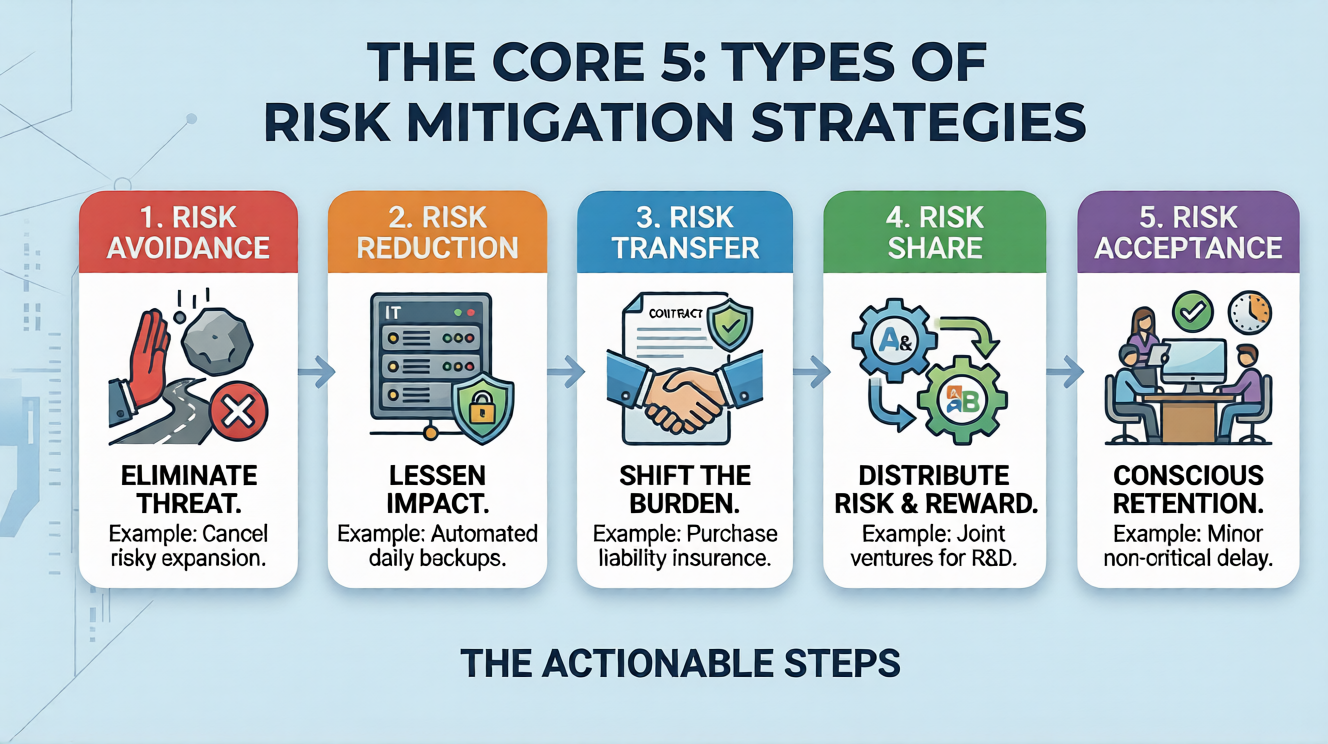
Once you have identified and assessed a critical business risk, you must decide exactly how to handle it. This is the heart of your Mitigation Planning. While the specific tactics will vary by industry, every response falls into one of five primary categories.
Here are the five core Risk Mitigation Strategies you can deploy to protect your projects:
1. Risk Avoidance: Sometimes the best defense is simply not playing the game. Risk avoidance involves completely eliminating the threat by altering your project scope, timeline, or strategy so that the risk no longer exists.
- Example: If a planned expansion into a new overseas market reveals extreme political instability and high financial risk, the avoidance strategy would be to cancel the launch in that specific region entirely.
2. Risk Reduction (Control): This is the most common of all Risk Mitigation Strategies. Risk reduction means you acknowledge the threat and take specific preventative actions to lessen either the probability of the event occurring or the severity of its impact if it does.
- Example: To reduce the probability of a catastrophic server failure (a major business risk), an IT department might implement automated daily backups and install redundant power supplies. The risk still exists, but the potential damage is drastically controlled.
3. Risk Transfer: Risk transfer does not eliminate the threat; instead, it shifts the financial or operational burden of that risk to a third party. This strategy is highly effective for risks that have a low probability but a potentially devastating financial impact.
- Example: Purchasing comprehensive liability insurance is the most classic form of risk transfer. Another example is outsourcing a highly specialized, dangerous, or complex operational task to an external vendor who assumes the liability.
4. Risk Acceptance (Retention): Not every risk requires a massive, expensive response. Risk acceptance is the conscious, documented decision to do nothing. This strategy is typically chosen when the probability and impact of the threat are very low, or when the cost of implementing other Risk Mitigation Strategies exceeds the potential cost of the risk itself.
- Example: A software development team might accept the risk of a minor, one-day delay on a non-critical feature update because reallocating resources to prevent the delay would disrupt the launch of their core product.
5. Risk Sharing: Similar to transfer, risk sharing involves distributing the burden of the threat—but in this case, the risk (and often the potential reward) is shared among multiple invested parties.
- Example: Two competing tech companies might form a joint venture to fund the research and development of an expensive, highly experimental new technology. By sharing the investment, they effectively halve their individual financial exposure if the project fails.
Best Risk Mitigation Templates for Professional Presentation
Communicating your comprehensive risk management strategy to stakeholders is just as critical as developing the plan itself. To secure executive buy-in and align your team, you must present your Risk Mitigation Strategies with absolute clarity and authority.
Building a detailed risk matrix or a mitigation roadmap from scratch is incredibly time-consuming. More importantly, generic presentation templates and basic visual dashboards rarely offer the professional depth required for high-stakes business risk reporting. Standard bullet points simply cannot convey the logical hierarchies needed to persuade stakeholders of your preparedness.
Here are the top recommended templates to present your plan like a PRO:
Risk Mitigation Strategies Template

View: Risk Mitigation Strategies
Equip your team with WinSlides comprehensive Risk Mitigation Strategies Template, a fully editable presentation suite designed to visually articulate your entire risk management process for maximum executive impact. Replacing confusing spreadsheets with structured, easy-to-digest visual dashboards, this template features detailed action tables, management cycle infographics, and mitigation tactic flowcharts. Seamlessly compatible with both PowerPoint and Google Slides
Performance Management Template

View: Performance Management Template
Track the ongoing success of your risk response plans with WinSlides Performance Management Template, an essential tool for the critical monitoring and review phase of your strategy. Perfect for demonstrating team accountability and the effectiveness of your preventative actions over time, this suite features clean, chronological process timelines and step-by-step performance tracking graphics.
Final Words
Proactive mitigation planning is the engine that drives true business resilience. In a volatile market, you cannot afford to let uncertainty derail your hard work. By identifying threats early, assessing their impact, and deploying targeted Risk Mitigation Strategies, you transform potential disasters into manageable variables.
Don’t let a generic presentation undermine your strategic planning. Stop presenting like an amateur and start presenting like a PRO. Browse our specialized corporate templates at Winslides today to visualize your proactive risk strategies and command authority in your next critical meeting.
Related Blogs
-
Presentation tips February 4, 2026
7 Effective Presentation Techniques | Secret Presentation Skills, Tips and Techniques
How to Give a Killer Presentation? Secrets Revealed! Have you ever watched a world-class speaker and thought, “They were just born for the stage”? Most people believe that commanding a room is a rare personality trait—something you either have or you don’t. But here is the secret: Great presenters aren’t born; they are engineered. Behind…
-
Powerschool February 14, 2026
How to Start a PowerPoint Presentation: 7 Strong Opening Strategies for Success
Stop Boring Your Listeners: Dynamic Ways to Begin Your Next PowerPoint Presentation There is nothing more intimidating than a blinking cursor on a blank white slide. You know your topic inside and out. You have done the research. Yet, when it comes time to design that first slide and plan your opening remarks, you freeze….